What is RCE bug type?
 Sarah Richards
Sarah Richards What are RCE attacks?
Remote code execution (RCE) attacks allow an attacker to remotely execute malicious code on a computer. The impact of an RCE vulnerability can range from malware execution to an attacker gaining full control over a compromised machine.What is the purpose of RCE?
Functions of an RCERCEs bring together institutions at the regional/local level to jointly promote ESD. They build innovative platforms to share information and experiences and to promote dialogue among regional/local stakeholders through partnerships for sustainable development.
What is RCE CVE?
Today, researchers found a new HIGH vulnerability on the famous Spring Cloud Function leading to remote code execution (RCE). The vulnerability CVE-2022-22963 would permit attackers to execute arbitrary code on the machine and compromise the entire host. After CVE 2022-22963, the new CVE 2022-22965 has been published.What is RCE report?
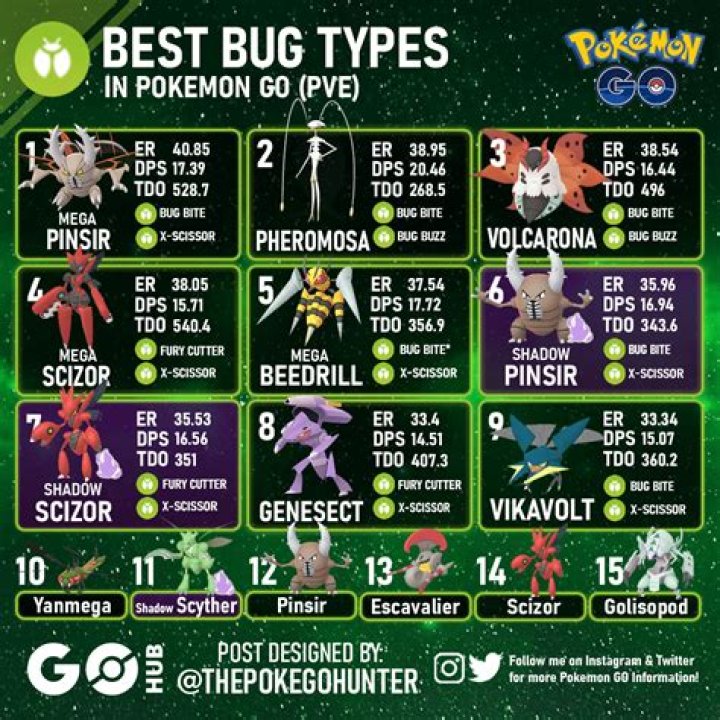
A Reconstruction Cost Estimate (RCE) is a figure that insurance companies use to estimate the cost of rebuilding your home in the case it gets completely destroyed.The Bug Type Sucks.
What is a 360 value?
360Value is a complete insurance-to-value solution for the property insurance industry. Based on unparalleled information and advanced technology 360Value will provide you with the best replacement cost estimates available.What is reconstruction cost?
Reconstruction cost value is the cost to replace or rebuild a home to original or like standards at current material and labor costs within a certain geographical area. Meanwhile, a home's market value is the price a consumer is willing to pay for the home.What is spring RCE vulnerability?
The Spring4Shell RCE vulnerability allows attackers to execute code on applications using the Spring framework before 5.3. 18 or 5.2. 20 , with JDK 9+ . In addition, applications need to be mapping request parameters into Plain Old Java Objects (POJO) to be vulnerable.How do I fix Spring4Shell vulnerability?
4 ways to fix Spring4Shell Vulnerability
- JDK 9 or higher.
- Apache Tomcat as the Servlet container.
- Packaged as a traditional WAR (in contrast to a Spring Boot executable jar).
- spring-webmvc or spring-webflux dependency.
- Spring Framework versions 5.3. 0 to 5.3. 17, 5.2. 0 to 5.2. 19, and older versions.
What is remote code injection?
Code Injection, also known as Remote Code Execution or Code Evaluation, involves modifying an executable or script containing malicious code. Hackers first probe the application for attack surfaces that can accept untrusted data and use it when executing program code.What is RCE engineering?
RCE stands for Registered Civil Engineer.What is RCE sustainability?
An RCE is an existing formal, non-formal and informal organization that facilitates learning towards sustainable development in local and regional communities. As of December 2018, 168 RCEs have officially been acknowledged by the United Nations University worldwide.Is remote code execution A vulnerability?
One well-known vulnerability in web applications is one that is known as Remote Code Execution. In this type of vulnerability an attacker is able to run code of their choosing with system level privileges on a server that possesses the appropriate weakness.What are the 4 main types of vulnerability?
The different types of vulnerabilityIn the table below four different types of vulnerability have been identified, Human-social, Physical, Economic and Environmental and their associated direct and indirect losses.
What is a remote exploit?
A remote exploit works over a network and exploits the security vulnerability without any prior access to the vulnerable system. A local exploit requires prior access to the vulnerable system and usually increases the privileges of the person running the exploit past those granted by the system administrator.Why is buffer overflow A vulnerability?
Key Concepts of Buffer OverflowThis error occurs when there is more data in a buffer than it can handle, causing data to overflow into adjacent storage. This vulnerability can cause a system crash or, worse, create an entry point for a cyberattack. C and C++ are more susceptible to buffer overflow.
Is Spring boot vulnerable to Spring4Shell?
If the application is deployed as a Spring Boot executable JAR (the default method) it is not vulnerable to this specific exploit. However, while no other exploits are identified at the time of writing, they are theoretically possible due to the nature of the vulnerability.Does Spring4Shell affect Java 8?
Java 8 does not appear to be vulnerable. So far, the only confirmed exploit depends on Spring being deployed with TomCat. However, other vectors may be discovered. We recommend all Spring users update, starting with those using TomCat.What is CVE-2022-22965?
CVE-2022-22965 DetailA Spring MVC or Spring WebFlux application running on JDK 9+ may be vulnerable to remote code execution (RCE) via data binding. The specific exploit requires the application to run on Tomcat as a WAR deployment.